When you connect to a VPN, all of your internet traffic is routed through an encrypted ‘tunnel’ between your device and the VPN server. But how is this ‘tunneling’ accomplished?
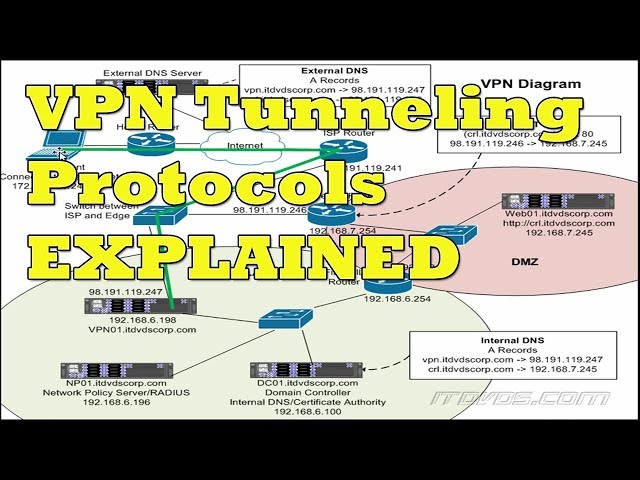 Checkout this video:
Checkout this video:
Introduction
Tunneling is a technique used to encapsulate Internet Protocol (IP) datagrams within Internet Protocol packets. The technique allows an organization to use the public infrastructure, such as the Internet, to securely connect private internal networks. Private internal networks are usually behind a firewall and NAT router. To tunnel datagrams, special tunneling software wraps the private network IP datagrams with a public IP header. This wrapping process is transparent to users.
There are two types of tunneling: voluntary and compulsory. Voluntary tunneling is initiated by the user’s computer, while compulsory tunneling is initiated by the network administrator. Once a connection is made, data can be sent through the tunnel to the private network.
What is ‘Tunneling’?
In computing, tunneling refers to a technique used to manage and secure communication between computer networks that are not necessarily trusted. It involves encapsulating data in one network protocol (the “carrier”) so that it can be transported over another network protocol (the “tunnel”). The data is then decapsulated at the receiving end, and the original message can be read.
Tunneling is commonly used to secure communications between two networks that are not trusted, such as a corporate network and the public Internet. It can also be used to allow members of a virtual private network (VPN) to access resources on a shared or public network, such as the Internet. In this case, the VPN tunnel securely connects the VPN client on the user’s computer to the VPN server on the company’s network.
How is ‘Tunneling’ Accomplished in a VPN?
tunneling is the process of encapsulating one protocol within another. The most common type of tunneling is when an Internet Protocol (IP) datagram is encapsulated within an IP packet. This is how a VPN is able to send data over a public network while still keeping it secure.
The ‘Tunneling’ Process
When you connect to the internet, your computer or mobile device sends out small pieces of data called ‘packets.’ Each packet contains information about where it is supposed to go and how to get there.
Normally, your packets travel directly from your device to the destination server, and then back again. But when you use a VPN, your packets travel through an intermediary server before reaching their destination. This process is known as ‘tunneling.’
Tunneling allows your packets to bypass restrictions and firewalls that may be in place on your network or the network you’re trying to connect to. It also encrypts your traffic, making it harder for anyone to snoop on what you’re doing online.
Conclusion
Tunneling is the process of encapsulating data within other data so that it can be transmitted over a network. In the context of a VPN, tunneling refers to the process of encapsulating data traffic from one network and sending it over another network (usually the public internet) so that it appears to be coming from the VPN server. By tunneling data traffic through a VPN, businesses can ensure that their data is transmitted securely and privately.
